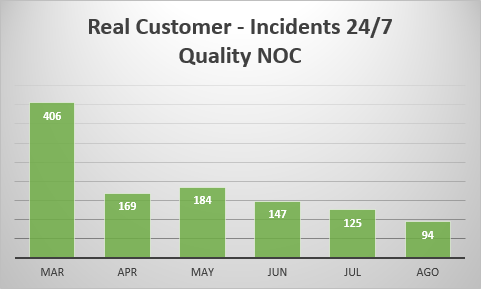
Yes, buy the time you need, hire Quality NOC
We have a TEAM of experienced System Administrator that can take over many of your task and FREE UP the time of your Operations Team.

Key benefits of outsourcing NOC services
- Significant reduction in downtime
- Immediate management of incidents occurring around the clock
- Reduced Operational costs
- Increased productivity and job satisfaction for your network and IT support staff
- Free up your IT resources
- Increased end-user / customer satisfaction
- Reduced managerial/HR time and effort
- 24x7x365 High Availability support
Contact us today,
[contact_bank form_id=1 show_title=true show_desc=false]